Wargaming a China-Taiwan Conflict and Its Cyber Scenarios
China’s use of cyber strategies in a conflict with Taiwan is likely to follow a methodical, gradual approach
This post is co-authored by the Predictive Defense and Natto Thoughts.
Since the start of his second term in January 2025, the Trump administration has conducted military actions or strikes in seven countries. The ouster of Venezuelan president Nicolas Maduro in January 2026 and the ongoing US-Israeli joint military operation against Iran makes it feel as if the threshold for war has been lowered. Leaders across the globe are likely drawing their own conclusions. Bill Bishop, a China expert at Sinocism, remarked, “Maduro and now Ayatollah Ali Khamenei in two months. Would love to know what Xi really thinks about this,” referring to Chinese President Xi Jinping. Indeed, what does Xi think about these developments? In particular, how do they shape Xi’s views on Taiwan “reunification”? Have US military actions in seven countries influenced Xi’s perspective on using military force to achieve China’s goal of “reunification”—which he considers a “historical inevitability”?
A potential conflict between China and Taiwan would represent a globally significant inflection point. Drawing from the Center for Strategic and International Studies (CSIS) 2023 report The First Battle of the Next War: Wargaming a Chinese Invasion of Taiwan, this piece aims to conduct a reality check on a likely scenario of China-Taiwan conflict presented in the CSIS report, and examines the challenges and possible cyber implications of such a scenario and how organizations across sectors could be exposed, whether directly or indirectly.
Based on war games involving a simulated invasion, the CSIS study provides insights under clearly defined assumptions, including participating actors and their roles, mobilization timelines, ammunition availability and the type of operations conducted. While no single study can predict outcomes, its transparent methodology and multi-scenario approach provide a useful analytical foundation.
Four Potential Winning Conditions and Challenges That Could Create Openings for China
The CSIS study analyzes 24 iterations of a large-scale war game simulating a Chinese amphibious invasion of Taiwan. It focuses primarily on conventional military variables such as force posture, logistics, attrition, alliance coordination, and operational timelines under varying assumptions. Across most scenarios, Taiwan avoids defeat only with active US intervention and access to Japanese bases. Even then the cost is severe for all sides: heavy naval and air losses, high casualties, and significant economic disruption. Cyber operations are not treated as a decisive variable in the simulations, but the report remains valuable for understanding the conditions that are crucial for Taiwan’s defense.
The CSIS study identifies the critical conditions required for Taiwan and its partners to prevail. From an adversary’s perspective, these conditions highlight the pressure points China would likely attempt to disrupt before or during a conflict, with cyber operations serving as one of the enabling tools. We will examine four key conditions for success identified in the CSIS report and apply adversarial perspectives to consider challenges to these winning conditions that could provide openings for China. This does not imply that China will pursue these actions, nor that cyber capabilities would be the primary means. Rather, the exercise helps frame where cyber-enabled activity could plausibly emerge.
1. The Need for Taiwanese Ground Forces to Contain the Landing
The CSIS report emphasizes that Taiwan’s ground forces are decisive in preventing a successful lodgment and breakout. However, these forces exhibit structural weaknesses, particularly in manpower and readiness.
Sustained ground defense is fundamentally a numbers and endurance challenge. Based on our assessment, two key pressure points emerge:
Conscription and force generation: The ability to mobilize, train and rotate sufficient personnel over time is critical to maintaining front-line effectiveness and replacing losses in a prolonged conflict.
Ammunition stockpiles and production capacity: Having adequate reserves and the industrial capability to restock munitions at a rate that matches battlefield consumption.
Challenges: As the CSIS report points out, Taiwan’s ground forces have faced difficulties in filling positions, resulting in a reduction of the army’s size from 200,000 in 2011 to 94,000 in 2022. To boost manpower, at the end of 2022 former President Tsai Ing-wen announced a plan to realign Taiwan’s military force structure, including extending the conscription period from four months to a full year beginning in 2024. However, an April 2025 report from The Diplomat, a Washington, D.C.-based Indo-Pacific region-focused online news magazine, indicates that “with understocked equipment, lackluster recruitment, and budget fights in the legislature, full implementation of Taiwan’s new mandatory military service plan remains difficult.”
2. The Need for Pre-Supplied Weapons from the US and Allies
Taiwan’s ability to resist depends heavily on weapons being delivered before conflict begins. This requirement hinges on:
Financing and procurement mechanisms: The availability of funding and the efficiency of acquisition processes to secure and deliver needed systems in a timely manner.
Political willingness in the United States and allied countries: The readiness of governments to approve, prioritize and sustain arms transfers despite competing domestic and strategic considerations.
US risk tolerance for escalation is a decisive variable, as efforts to pre-position or accelerate weapons deliveries before a conflict could themselves be perceived as escalatory. This affects how far the US is willing to go in advancing support timelines, given the risk of provoking a response or raising tensions prior to the outbreak of hostilities.
Challenges: Since 2020, as China has increased military provocations against Taiwan, Taiwan has strengthened its defense by expanding its weapons stockpiles with a special military budget in 2021 and meeting its missile production goals two years ahead of schedule. However, Taiwan’s current production rate—about 1,000 precision missiles per year—is not sufficient to stop a full-scale Chinese invasion, and its stockpile could be depleted in just a few days, as reported by Asia Times, a Hong Kong-based news outlet, in August 2025.
Although the United States is Taiwan’s closest arms provider, US arms sales have often been delayed due to competing geopolitical priorities. Taiwan is also seeking to co-produce munitions and weapon systems with the US, but this effort remains in the planning stages.
3. The Need for Japanese Base Access
US access to its military bases in Japan is a critical operational requirement. This is a legal and political decision for Tokyo, as it depends on Japan’s willingness to authorize the use of its territory for combat operations and accept the associated risks.
Challenges: As the CSIS report points out, Japan hosts more US bases and service members than any other state in the world. In 2025, approximately 55,000 US military personnel were stationed in Japan. The US State Department has described the security cooperation with Japan as “the cornerstone of peace, stability, and freedom in the Indo-Pacific region.” In any response to a Chinese invasion, the US would rely primarily on its bases located in Japan, due to “the proximity of these bases to Taiwan and the lack of nearby alternatives,” according to the CSIS report. Over the years, some political groups in Japan have protested against US bases but have carried little weight in government policy.
4. The Need for US Political Willingness to Sustain High Losses
Even if military conditions are favorable, US willingness to absorb heavy losses and continue fighting is a central determinant of outcome. Based on our assessment this depends on political leadership and public support holding firm as casualties mount, which can become increasingly difficult over time.
Challenges: The CSIS report concludes that US involvement in fighting a Chinese invasion of Taiwan would likely result in high losses, potentially damaging the US’s global position for many years. Although former US President Joe Biden promised to defend Taiwan against attack, implying a willingness to sustain such losses, the current US administration has sent mixed messages.
When these preconditions and potential countermeasures are viewed collectively, a coherent set of probable Chinese objectives emerges - objectives that China may pursue to facilitate its goal of “reunification”:
Degrade Taiwan’s ability to sustain ground resistance by weakening manpower mobilization, ammunition availability, and battlefield communications.
Erode US and allied pre-conflict preparation by reducing political willingness to arm Taiwan in advance.
Fracture alliance cohesion by increasing political hesitation in Japan and other regional partners regarding direct involvement.
Undermine domestic political will in the United States to sustain a prolonged, high-casualty conflict.
In essence, China’s objectives would be to shape the strategic environment so that Taiwan’s coalition cannot mobilize, coordinate, or sustain resistance at the required scale. Information operations1, – including cyber operations (also known as computer network operations) and influence operations (also known as psychological operations) – would likely serve as enabling instruments in support of these broader political and military goals.
The two critical roles that the US Cyber Command played in the most recent US-Israeli operations exemplify how cyber instruments could enable military goals. US General Dan Caine explained at a press conference on March 2, 2026, approximately 57 hours after the operations began, that along with US Space Command, US Cyber Command was among the “first movers” that were “layering non-kinetic effects, disrupting, degrading, and blinding Iran’s ability to see, communicate, and respond,” which “shaped the environment for the subsequent phases of the operation.” He further stated that US Space Command and US Cyber Command “have continuously layered effects to disrupt, disorient, and confuse the enemy.”
How China Will Likely Use Cyber Means to Facilitate its Strategic Goals
Over the years, China has been undertaking methodical, gradual steps aimed at shaping the strategic environment. This has become more overt since 2015. A significant turning point was the revelation in May 2023 that Chinese state threat group Volt Typhoon had targeted US critical infrastructure. Subsequently the US government officially reported on Volt Typhoon following the US Department of Justice (US DoJ)’s takedown of a botnet allegedly used by Volt Typhoon in January 2024. US officials pointed out that China’s “historical focus on stealing state secrets and espionage,” meaning cyber espionage for political and economic interests, has evolved into a more ominous intention to prepare for destructive attacks. As US officials said, Volt Typhoon campaigns show “a new interest in preparing and launching destructive cyberattacks against US electricity systems, water utilities, military organizations and other critical services,” and the intent is to “cause disruption and sow societal panic, especially in the event of a military conflict.”
If China, indeed, is preparing for and pre-positioning the country for any kind of military conflict using cyber means – such as if the US military helped Taiwan resist a potential Chinese attack – this makes us wonder what China’s next move will be. As we know, cyber activities for the purpose of pre-positioning can also be a form of deterrent, such as to make the US think twice about coming to the aid of Taiwan. Influencing the US policy-making process or stealing intellectual property through cyber espionage to further China’s strategic goals also likely remain on the regular Chinese threat activity agenda.
Therefore, examining possible scenarios of Chinese information operation activities in the following categories—both in preparation for and during a military conflict with Taiwan—may help us better understand how China would likely use cyber means to facilitate its strategic goals.
Cyber-enabled Influence operations
Increased bot activity targeting social media platforms, messaging apps, online games as well as gaming forums with large Taiwanese or Japanese user bases, such as social media platform LINE
Account takeover attempts, phishing or impersonation attempts targeting influencers in Japan and Taiwan who are vocally anti-China
DDoS and other disruption attempts targeting online news websites that are vocally anti-China
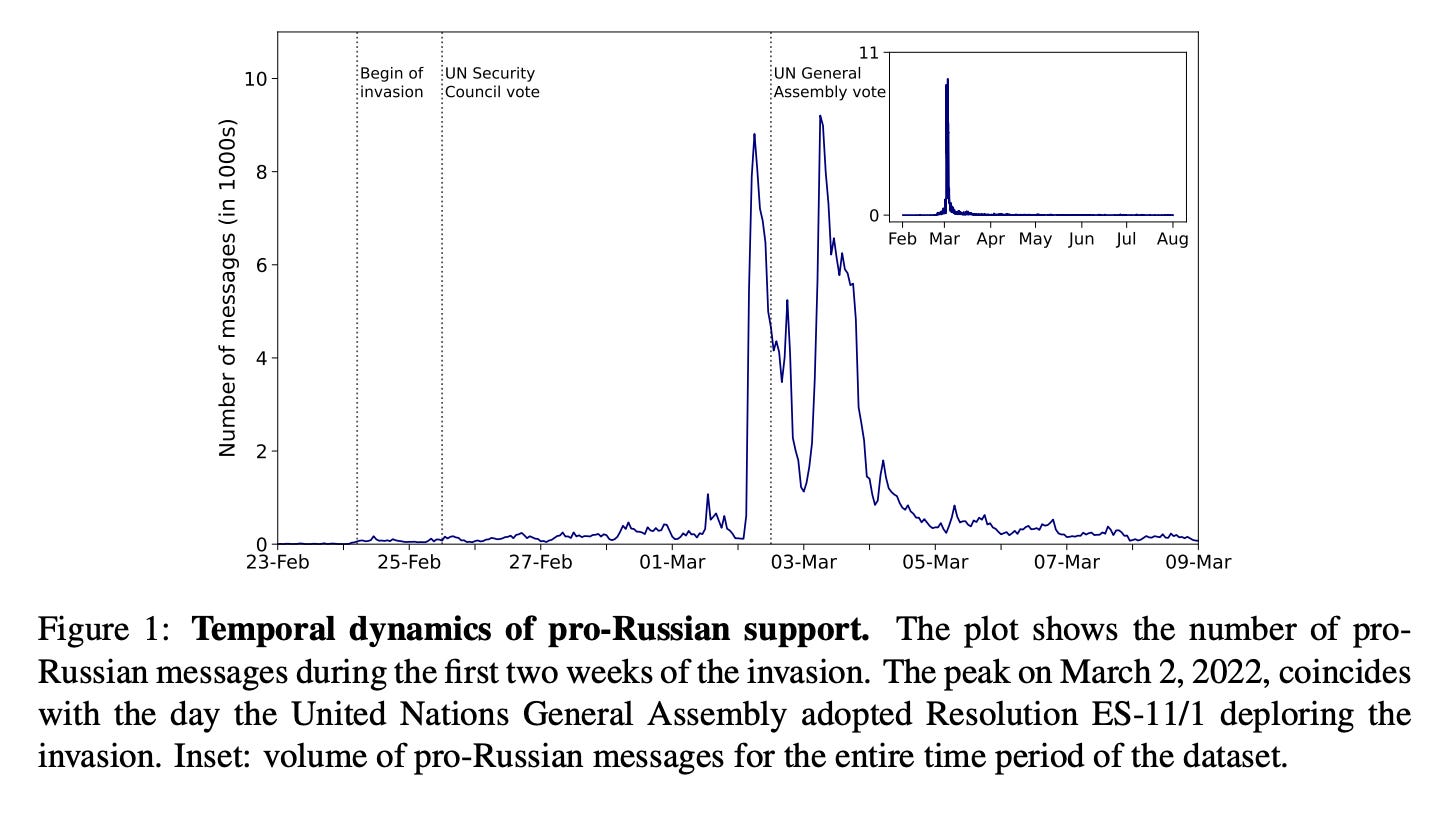
These are typical activities associated with mass disinformation campaigns, the topic of a series of Natto Thoughts posts, including case studies of their use by China and Russia. Before and during a conflict, a huge volume of bot activity — often amplified with the help of Large Language Models — would likely be unleashed in an attempt to control the online narrative. As in the case of Russia, messages are likely to be disseminated not only on the social media giants, but also on more localized forums, blogs, games and messaging apps. An academic study about Russian propaganda on social media during the 2022 invasion of Ukraine written by several German scholars shows that the peak on March 2, 2022, coincides with the day the United Nations General Assembly adopted Resolution ES-11/1 deploring the invasion, likely intended to sway the votes of the UN delegates. (See chart below)
Hacktivist activities
DDoS and other low-impact hacktivist activities, such as defacement attacks targeting government websites of the US, Japan and Taiwan and banking sectors
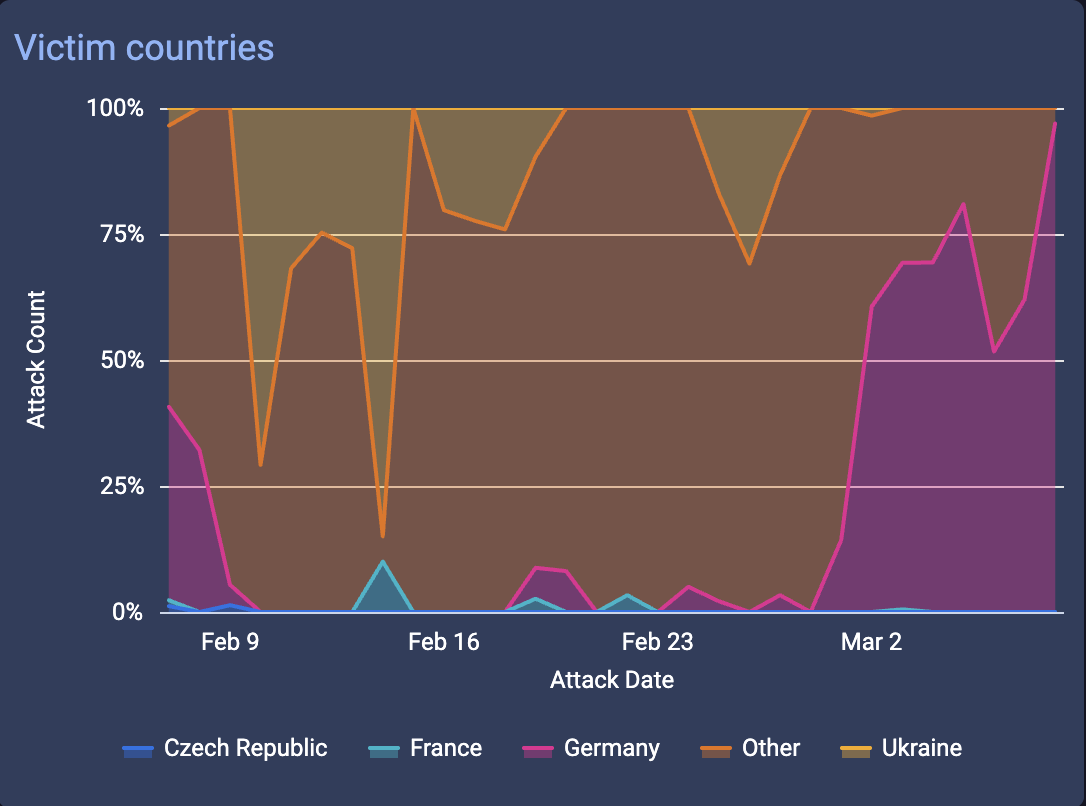
This is also typical with conflicts. Low-tier hacktivist groups want to grab the headlines and demonstrate their patriotism through attacks on government and banks of enemy countries. For example, the share of DDoS targets located in Germany rose from 5% to 70% after the US-Israel operation on Iran in late February 2026, according to data from VirusTotal, a US-based threat intelligence aggregator (see chart below). This shift likely reflects Germany’s public stance in support of Israel during the conflict, which may have increased its visibility as a target for hacktivist groups seeking symbolic or attention-grabbing targets rather than conducting coordinated disruption. While many of China’s first generation of patriotic “red hackers” or “honkers” have graduated from hacktivism to providing sophisticated cyber services for the state, further hacktivist activities in support of China against Taiwan cannot be excluded.
Cyber espionage operations
Intrusion and data exfiltration attacks targeting survey and polling companies researching public opinion in Taiwan and Japan
Intrusion attacks targeting government IT contractors in the US, Japan, and Taiwan, particularly those developing back-office software.
News reporters, think tanks and public opinion research companies are persistent targets for cyber espionage. However, during wartime these intrusions often become part of broader harassment campaigns aimed at shaping the narrative surrounding the war. For example, the Institute of Mass Information, a civil society organization based in Ukraine, reported in July 2024 that Russia committed 607 crimes against journalists and the media in Ukraine in the two years and five months since the start of the full-scale invasion. Government contractors are also persistent targets of cyber espionage given their broad access to government networks.
Offensive cyber operations
Pre-conflict intrusion activity and potential disruptive cyberattacks during conflict targeting civilian energy and telecommunications providers supporting US bases in Japan
Ransomware or pseudo-ransomware attacks targeting Tier-2 and Tier-3 industrial suppliers critical to defense production
Ransomware attacks targeting Japanese automotive manufactures and major suppliers to signal economic pressure.
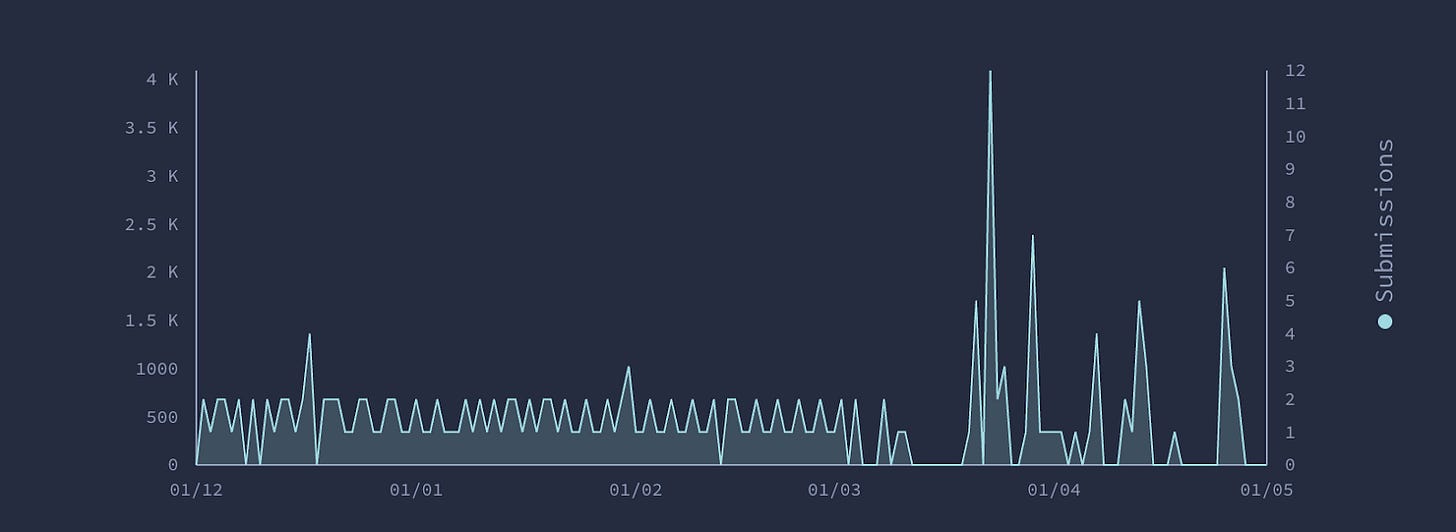
As the Natto Team has pointed out in the case of Russia, analysts have discerned a “playbook” combining disruptive and destructive operations with psychological operations. Indeed, evidence suggests that ransomware can serve as a form of hybrid warfare. In China, too, threat actors with some degree of relationship to the Chinese state have used ransomware to cause misattribution, distraction, disruption or even destruction and to provide financial gain, cover for espionage operations and the ability to remove the evidence. During the Russia-Ukraine conflict in 2022-2023 several cybersecurity firms observed disruptive campaigns against industrial and economic sectors, along with an evolution of toolsets better suited for disruptive operations. For example, US based cyber firm Mandiant, now part of Google Cloud, discovered that APT44 (a.k.a Sandworm) demonstrated tooling evolution during its wartime operation. VirusTotal also showed a spike of malware and Indicators of Compromise (IoC) submissions from December 2021 to May 2022, the months leading up to the full-scale Russian invasion of Ukraine. (See chart below)
Overall, these possible scenarios of using cyber means to facilitate China’s strategic goals in the China-Taiwan conflict are likely to evolve as geopolitical situations, the development of military technologies, and the understanding of military conflicts progress. As Nikita Shah, a senior fellow at the Center for Strategic & International Studies (CSIS), pointed out, in the ongoing US-Israel and Iran conflict in March 2026, cyber operations are “not a revolutionary edge in conflict,” but rather incremental. For China, “reunification” with Taiwan is seen as inevitable and “unstoppable”. Therefore, China is likely to act strategically, using cyber operations to achieve steady, incremental progress toward its objectives.
Information operations (IO) refers to the integrated employment, during military operations, of information-related capabilities in concert with other lines of operation to influence, disrupt, corrupt, or usurp the decision-making of adversaries and potential adversaries while protecting our own, according to Joint Publication 3-13 Information Operation, 27 November 2012 published by the US Department of Defense. The core capabilities include capabilities, such as Electronic Warfare, computer network operations, psychological operations, military deception, and operations security. The Natto Team has written extensively about information operations as a form of hybrid warfare.